Sonar's latest blog posts
Building Confidence and Trust in AI-Generated Code
To tackle the accountability and ownership challenge accompanying AI-generated code, we are introducing Sonar AI Code Assurance

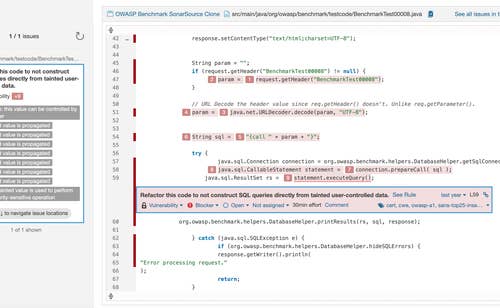
What is 'taint analysis' and why do I care?
In large systems, finding the bad actors is easier said than done. First you have to find all the places you accept data from users, and then you have to sanitize the data before you use it. The hard part is making sure you've found all the sources of user data and intervened before any kind of use. That's where taint analysis comes in.
Read Blog post >

The state of the copyleft license
In this post, I want to go a little deeper into one important type of license: those that require sharing of modifications under certain conditions, often called “copyleft” or “reciprocal” licenses
Read article >
Get new blogs delivered directly to your inbox!
Stay up-to-date with the latest Sonar content. Subscribe now to receive the latest blog articles.

WordPress <= 5.2.3: Hardening Bypass
This blog post details an authenticated Remote Code Execution (RCE) vulnerability in the WordPress core that bypasses hardening mechanisms. The vulnerability is present in the WordPress core in versions prior to 5.2.4
Read Blog post >
Clean as You Code: How to win at Code Quality without even trying
Analyzing a legacy project can be overwhelming. Learn how to Clean as You Code to make sure that the code you release into production tomorrow is at least as good as - and probably better than! - the code that's in production today.
Read Blog post >

Bit Rot: the silent killer
Your code is rotting right now. Every day, each one of your production services, internal tools, and open source libraries decays a little bit.
Read article >

Package management: a brief history
Application developers today are used to relying on and pulling in a number of open source libraries to help them focus on the functionality that’s important to their business.
Read article >

The simple magic of package manifests and lockfiles
If you aren’t using open source components to build your apps, you’re not living in 2019. Our research suggests 92% of professional applications are built using open source.
Read article >

Backend SQL Injection in BigTree CMS 4.4.6
BigTree is a small content management system which does not depend on many frameworks and advertises itself as user friendly and developer ready. In this blog post, we will take a look at a few vulnerabilities we have detected in the codebase of BigTree.
Read Blog post >

How much time do developers spend actually writing code?
In this post, we share the third of eight key findings. If you don’t wait to wait for the rest of the results, you can download the full survey report right now at the link below.
Read article >
Drive By RCE Exploit in Pimcore 6.2.0
In this technical blog post we will examine how a drive by exploit in the Pimcore release 6.2.0 allows an attacker to execute OS commands.
Read Blog post >
WooCommerce 3.6.4 - CSRF Bypass to Stored XSS
WooCommerce is the most popular e-commerce plugin for WordPress with over 5 million installations. We detected a code vulnerability in the way WooCommerce handles imports of products.
Read Blog post >
