Sonar's latest blog posts
Announcing SonarSweep: Improving training data quality for coding LLMs
Recent research from Anthropic has shown that even a small amount of malicious or poor quality training data can have a massively negative impact on a model’s performance, exposing users to significant security and quality issues.


Our journey toward accessibility
When you think about your typical workday, how much time do you spend working on a computer? How hard would it be for you to perform your job if you did not have access to a computer?
Read Blog >
Securing Developer Tools: OneDev Remote Code Execution
We recently discovered several vulnerabilities in OneDev 7.2.9 that allowed attackers to fully compromise a server and even break out of a Docker environment.
Read Blog >
Get new blog posts delivered directly to your inbox!
Stay up-to-date with the latest Sonar content. Subscribe now to receive the latest blog articles.
Interview with a SonarSource Developer
Curious about life as a Developer at SonarSource? Join us as we discuss changes in the world of programming, the importance of Security, and writing code with SonarQube Cloud Backend Developer Claire Villard.
Read Blog >

The evolving landscape of open source licensing: What you need to know
In this post we will cover why it’s important to know what licenses accompany the open source in use at your organization
Read article >
The Power of Code Quality
Code Quality—a term you may have casually used or heard before but may not have synthesized or internalized its true essence. In this post, learn what Code Quality is and why it matters.
Read Blog >

WordPress Core - Unauthenticated Blind SSRF
Our security researchers were surprised to discover a low-hanging code vulnerability in WordPress Core that we will discuss in this blog post.
Read Blog >
You’re 3 minutes away from clean Java pull requests!
In this blog, we demonstrate how you can get started with SonarQube Cloud in less than 3 minutes and ensure all new Java pull requests are clean, every time.
Read Blog >

Sonar Streamlines the Race to Release
Knowing if your latest release candidate is built with Code Quality doesn’t have to be a guessing game. With Sonar at your side, you’ll know that every new line, every PR and every build is clean.
Read Blog >

Securing Developer Tools: Argument Injection in Visual Studio Code
In the third part of our Securing Developer Tools series, we look at a critical vulnerability that affects one of the most popular code editors: Visual Studio Code.
Read Blog >
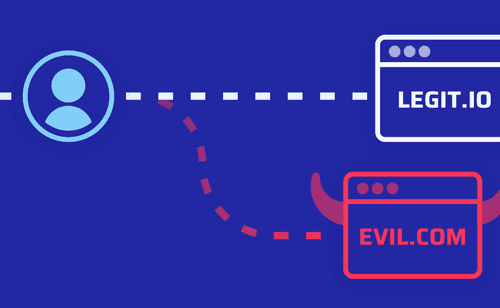
Security Implications of URL Parsing Differentials
Our security research led to the discovery of a flaw in a popular Apache2 authentication module. We come back on this case of parsing differential and how various languages behave when working with URLs.
Read Blog >

Disclosing information with a side-channel in Django
We recently found a vulnerability in Django that allows us to disclose sensitive information. Let’s review the root cause, exploiting technique, and patch.
Read Blog >